40 Common Cybersecurity Terms Every Beginner Should Know
When you start learning cybersecurity, understanding the terminology is half the battle. These terms are not just definitions you memorize—they are concepts you will see every day in real-world scenarios, tools, alerts, and interviews.
Let’s break each term down in a clear, paragraph-style format with simple explanations and practical examples.
1. Cybersecurity
Cybersecurity is the practice of protecting systems, networks, and data from digital attacks. It involves using technologies, processes, and controls to prevent unauthorized access, damage, or theft. In simple terms, it’s about keeping your digital world safe.
Example: A company uses firewalls, antivirus software, and monitoring tools to protect its internal network from hackers. That entire setup is part of cybersecurity.
2. Threat
A threat is anything that has the potential to cause harm to a system, network, or data. It doesn’t always mean an attack is happening, but it represents a possible danger.
Example: A hacker group targeting financial institutions is considered a threat, even before they launch an attack.
3. Vulnerability
A vulnerability is a weakness or flaw in a system that can be exploited by an attacker. These weaknesses can exist in software, hardware, or even human behavior.
Example: An outdated web server with known security issues is a vulnerability that attackers can exploit.
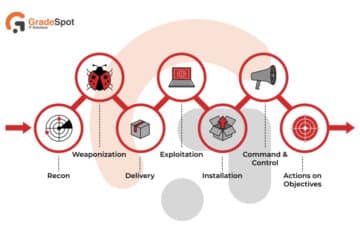
4. Exploit
An exploit is a method or piece of code used to take advantage of a vulnerability. It is how attackers actually break into systems.
Example: If a website has a SQL injection vulnerability, an attacker uses an exploit to run malicious queries and access the database.
5. Risk
Risk is the likelihood of a threat exploiting a vulnerability and the impact it would cause. It helps organizations decide what needs to be fixed first.
Example: If a critical server has a vulnerability and is exposed to the internet, the risk is high because attackers can easily target it.
6. Malware
Malware refers to any software designed to harm, exploit, or disrupt systems. It includes viruses, worms, ransomware, and spyware.
Example: Ransomware encrypts a company’s data and demands payment to restore access.
7. Phishing
Phishing is a type of attack where attackers trick users into revealing sensitive information like passwords or credit card details. It often happens through fake emails or websites.
Example: You receive an email that looks like it’s from your bank asking you to log in. The link takes you to a fake website that steals your credentials.
8. Social Engineering
Social engineering involves manipulating people into giving away confidential information. Instead of attacking systems, attackers target human behavior.
Example: An attacker calls an employee pretending to be from IT support and asks for login credentials.
9. Authentication
Authentication is the process of verifying a user’s identity before granting access to a system.
Example: Entering your username and password to log into your email account is authentication.
10. Authorization
Authorization determines what actions a user is allowed to perform after they are authenticated.
Example: An employee can view files but cannot delete them, while an admin has full access.
Master SOC Analysis
Are you passionate about cybersecurity and ready to build a career as a SOC Analyst? Look no further!
GradeSpot IT Solutions in Hyderabad offers expert-led training designed to make you industry-ready.
11. Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring more than one form of verification. This reduces the chances of unauthorized access.
Example: Logging in with a password and then entering a one-time code sent to your phone.
12. Encryption
Encryption is the process of converting data into a secure format so that only authorized users can read it. It protects data during storage and transmission.
Example: When you use a secure website (HTTPS), your data is encrypted while traveling over the internet.
13. Decryption
Decryption is the process of converting encrypted data back into its original readable form. Only authorized users with the correct key can decrypt the data.
Example: When you open a secure message, your system decrypts it so you can read it.
14. Hashing
Hashing is a process that converts data into a fixed-length value. Unlike encryption, it cannot be reversed, making it ideal for storing passwords securely.
Example: When you create a password, it is stored as a hash in the database instead of plain text.
15. Firewall
A firewall is a security system that monitors and controls network traffic based on rules. It acts as a barrier between trusted and untrusted networks.
Example: A firewall blocks unauthorized attempts to access your system from the internet.
16. Antivirus
Antivirus software detects, prevents, and removes malware from systems. It scans files and programs for malicious activity.
Example: Your system runs a scan and removes a detected virus from a downloaded file.
17. IDS (Intrusion Detection System)
An IDS monitors network or system activity and alerts administrators when suspicious behavior is detected. It does not block attacks but helps in identifying them.
Example: An IDS detects multiple failed login attempts and generates an alert.
18. IPS (Intrusion Prevention System)
An IPS not only detects threats but also takes action to block them in real time. It acts automatically to prevent attacks.
Example: An IPS blocks a malicious IP address after detecting suspicious traffic patterns.
19. VPN (Virtual Private Network)
A VPN creates a secure and encrypted connection over the internet, protecting user data and hiding their IP address.
Example: When using public Wi-Fi, a VPN ensures your data cannot be intercepted by attackers.
20. Endpoint
An endpoint is any device connected to a network, such as a laptop, mobile phone, or server. Endpoints are common targets for attackers.
Example: An employee’s laptop connected to a corporate network is considered an endpoint.
21. Patch Management
Patch management is the process of updating software to fix vulnerabilities and improve security.
Example: Installing the latest security updates on your operating system to prevent exploitation.
22. Zero-Day Vulnerability
A zero-day vulnerability is a security flaw that is unknown to the vendor and has no available fix. It is highly dangerous because it can be exploited immediately.
Example: Attackers discover a bug in software and use it before developers release a patch.
23. Zero-Day Attack
A zero-day attack occurs when attackers exploit a zero-day vulnerability before it is fixed.
Example: Hackers use an unknown browser vulnerability to gain access to user systems.
24. Brute Force Attack
A brute force attack involves trying multiple password combinations until the correct one is found.
Example: An attacker uses a script to guess passwords repeatedly until access is gained.
25. DDoS (Distributed Denial of Service)
A DDoS attack floods a system with massive traffic, making it unavailable to legitimate users.
Example: A website crashes because thousands of fake requests overwhelm the server.
26. SIEM (Security Information and Event Management)
SIEM tools collect and analyze logs from multiple sources to detect security incidents. They are widely used in SOC environments.
Example: A SIEM tool identifies unusual login behavior and alerts the security team.
27. SOC (Security Operations Center)
A SOC is a team responsible for monitoring, detecting, and responding to cybersecurity incidents.
Example: A SOC team investigates alerts generated by SIEM tools and takes action.
28. Incident Response
Incident response is the process of managing and handling a security breach or attack. It includes identifying, containing, and recovering from incidents.
Example: After detecting a breach, a team isolates the affected system and removes the threat.
29. Log Analysis
Log analysis involves reviewing system and network logs to identify suspicious activities or issues.
Example: Detecting repeated failed login attempts in server logs.
30. Penetration Testing
Penetration testing is a simulated attack performed to identify vulnerabilities in a system.
Example: Ethical hackers test a company’s website to find security weaknesses before attackers do.
31. Vulnerability Assessment
A vulnerability assessment is the process of scanning systems to identify potential security weaknesses.
Example: Using automated tools to detect outdated software and misconfigurations.
32. Threat Intelligence
Threat intelligence is information about current and potential threats that helps organizations defend against attacks.
Example: Receiving alerts about new malware campaigns targeting specific industries.
33. Data Breach
A data breach occurs when sensitive information is accessed or exposed without authorization.
Example: A database containing user passwords is leaked online.
34. Compliance
Compliance refers to following security standards, laws, and regulations to protect data.
Example: A company follows GDPR rules to protect customer data privacy.
35. Least Privilege
The principle of least privilege means users should only have access to what they need, nothing more.
Example: An employee can access only their department’s data, not the entire system.
36. Access Control
Access control is the process of managing who can access systems and resources.
Example: Only authorized users can log into a secure server.
37. Backup
A backup is a copy of data stored separately to recover in case of data loss or attacks.
Example: Restoring files from backup after a ransomware attack.
38. Cloud Security
Cloud security involves protecting data and applications hosted in cloud environments.
Example: Using security groups and firewalls to protect cloud servers.
39. Network Security
Network security focuses on protecting network infrastructure from unauthorized access and attacks.
Example: Using firewalls and IDS systems to secure a corporate network.
40. Application Security
Application security involves securing software applications from vulnerabilities and attacks.
Example: Fixing SQL injection issues in a web application.
Conclusion
Understanding these terms is like learning the alphabet of cybersecurity. Once you know them, everything else becomes easier—tools, concepts, interviews, and real-world problem-solving.
Don’t try to memorize everything at once. Instead, connect each term with a real-world scenario. That’s how you build real understanding, not just theoretical knowledge.




Informative blog
Much helpful to understand basic terminologies.